Your Private Journal That Stays Yours
Local-first journaling with mood tracking and AI insights — all on your device. No accounts, no cloud, no compromises.
Start writing in 10 seconds, nothing to install.
Windows, macOS, Linux. Full features. Always free.
See it in action
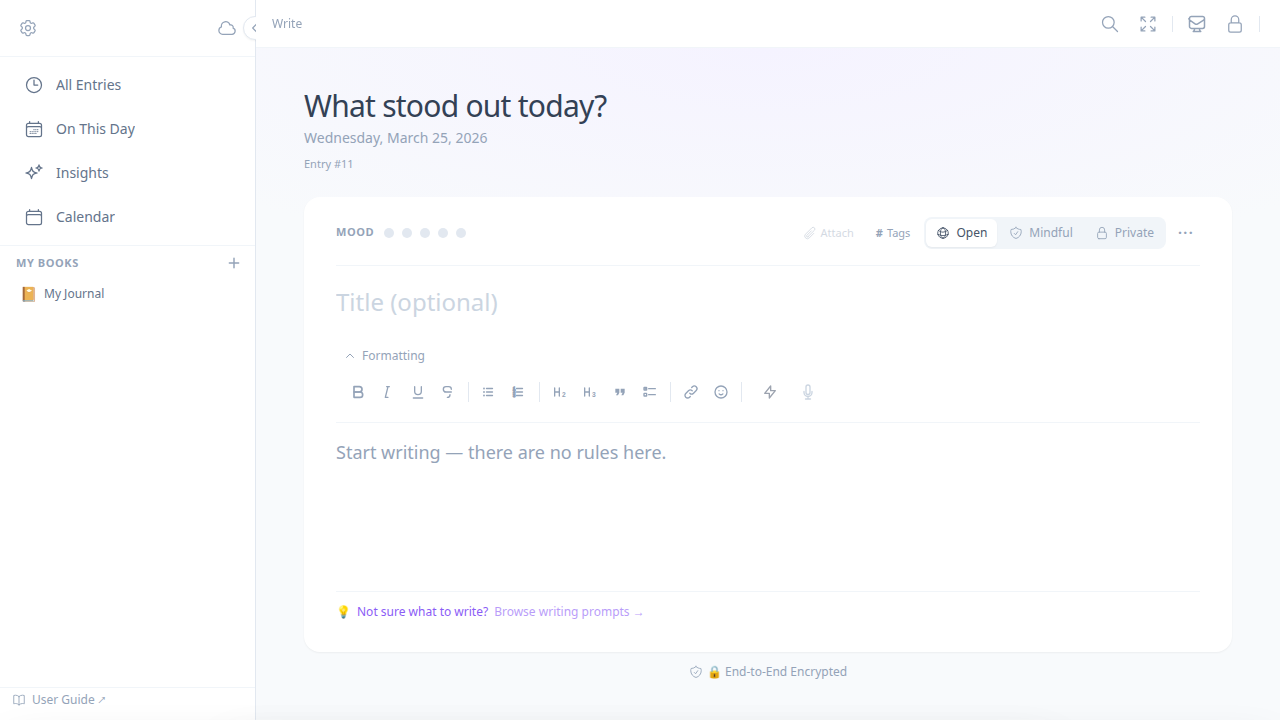
A writing space that respects you
Clean, focused, and private by default. Your words stay on your device.
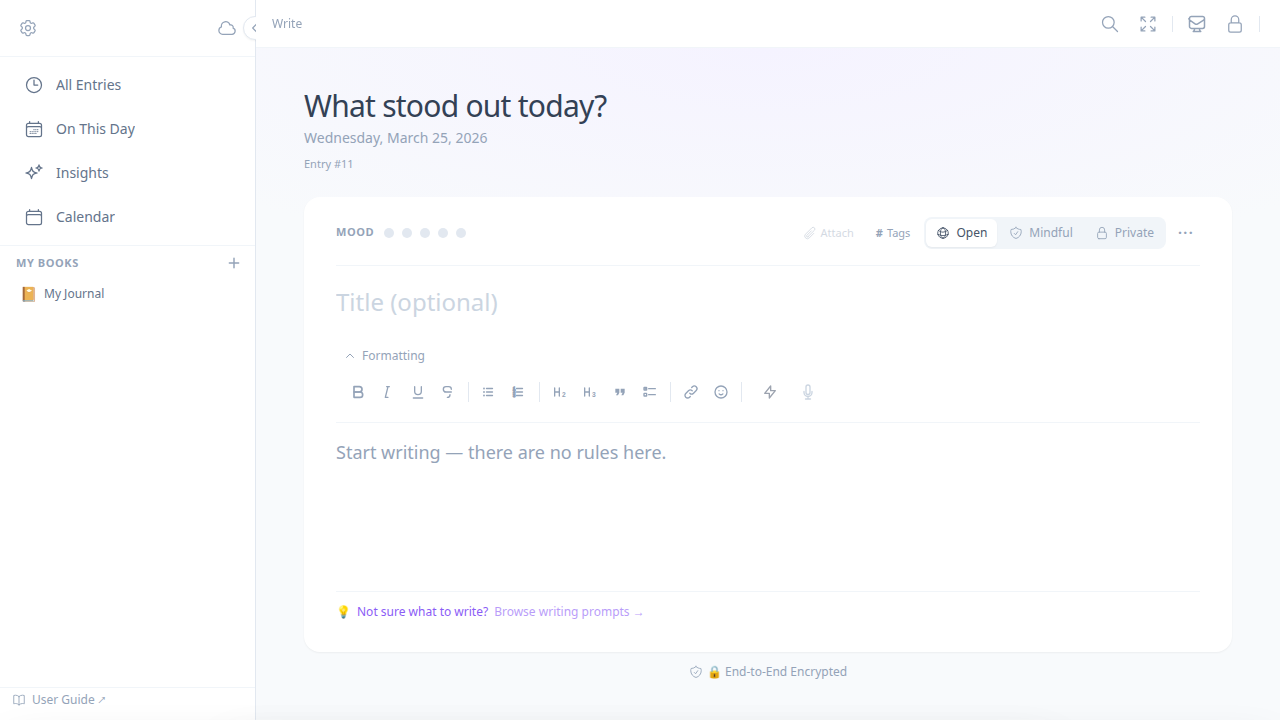
Write view
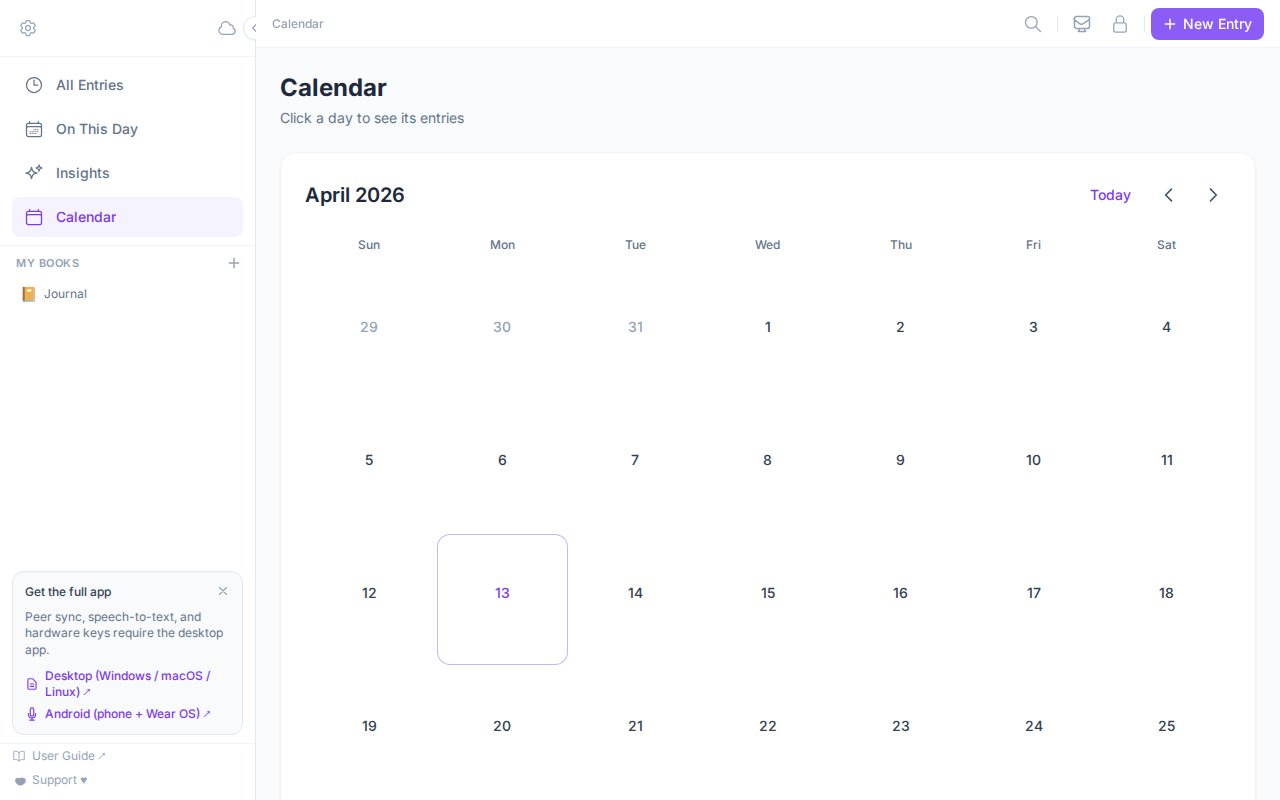
Calendar view
Mood selector
One tap to log how you feel. Five levels, always visible.
Rich text editor
TipTap-powered: headings, lists, bold, inline code. Yours locally.
Auto-save
Writes to encrypted SQLite the moment you pause. No manual save.
Multiple journals
Named books with emoji and color. Work, personal, therapy — separate.
Privacy at the core
Zero-knowledge
Your password is never stored or transmitted. Keys are derived in memory and cleared on lock.
No accounts
No email required. No tracking. No ads. Ever.
Open source
Every line of code is public on GitHub. You don't have to trust our privacy claims — you can verify them.
What you get
Everything you need, nothing you don't
Local-first, always
SQLite on your disk. No telemetry, no sync unless you opt in. Check the source — there's no network call in the entry save path.
AES-256-GCM encryption
PBKDF2, 600k iterations, per-entry random salt. Keys derived in memory, never stored. Audit it yourself in crypto.ts.
AI from metadata, not your words
Mood scores, time-of-day patterns, entry frequency — that's all the AI sees. Your journal text never leaves the device.
Multiple journals
Named books with emoji and color. Work, personal, therapy — each filtered separately in the timeline and calendar.
Peer sync over LAN
Ed25519 device identity, QR/PIN pairing, AES-256-GCM transport. No cloud relay. A passive observer sees only ciphertext.
Every platform
Native desktop on Windows, macOS, Linux. Browser PWA at journal.moodhaven.app. Wear OS for voice captures from your wrist.
Under the hood
Built to be verified, not trusted
Zero-knowledge by design
Your journal text never leaves your device. All encryption and decryption happens in the browser or desktop app using AES-256-GCM with PBKDF2-derived keys. The Rust backend stores and retrieves opaque ciphertext — it never sees plaintext.
Audit the source- Cipher
- AES-256-GCM
- Key derivation
- PBKDF2-HMAC-SHA256, 600k iterations
- Salt
- 16 bytes, per-entry random
- Key storage
- In-memory only, cleared on lock
- Cloud required
- Never
Privacy, proved
Zero data collected. Verified in code.
What we never collect
Not stored. Not transmitted. Not possible by design.
- Journal text
- Passwords or keys
- Usage analytics
- IP addresses
- Location (beyond opt-in weather)
- Device identifiers
Encryption spec
Verify it in crypto.ts and journal.rs.
- Cipher
- AES-256-GCMauthenticated encryption, tamper-evident
- Key derivation
- PBKDF2-HMAC-SHA256600,000 iterations — on par with 1Password and Bitwarden
- Salt
- 16 bytes, per-entry randomcompromising one key exposes exactly one entry
- Key storage
- Nonederived in memory, cleared on lock or exit
- Network calls on save
- ZeroSQLite write path is entirely local — audit create_journal_entry in journal.rs
- Source available
- MIT licensedevery line of the encryption path is public and auditable
Newsletter
Stay in the loop
Writing about privacy-first software, local-first design, and what's coming next. New posts go to Substack first.
Delivered via Substack. No spam. Unsubscribe any time.
MoodHaven is open source

- v1.1.0
- Current version
- 702
- Automated tests
- MIT
- License
- Mar 2025
- First commit
Built in public. Every line of code visible to you. MIT licensed.
View all articles on Substack